Security Practices to Protect Your Data in Cloud Storage Applications
Understanding the Importance of Data Security
Storage solutions have evolved significantly over the years, with cloud storage becoming a dominant method for data management among both individuals and businesses. The appeal lies in the convenience it affords; one can access vital documents from virtually anywhere, at any time. However, this ease of access is accompanied by significant security concerns that must be taken into account.
The digital landscape is littered with instances of data breaches and cyber-attacks. According to a report by Verizon, over 5,000 data breaches were recorded in the United States in the last year alone, affecting millions of personal and corporate accounts. Recognizing the inherent vulnerabilities in cloud storage necessitates proactive measures to shield sensitive information. Here are essential practices to enhance your data security:
- Strong Passwords: The foundation of data security starts with robust passwords. Avoid easily guessable passwords such as “123456” or “password.” Instead, use a combination of upper and lower-case letters, numbers, and special characters to create passwords that are at least 12 characters long.
- Two-Factor Authentication: This additional security layer requires not only your password but also a second form of verification, such as a text message or authentication app code. This measure significantly reduces the risk of unauthorized access, even if your password is compromised.
- Encryption: Data encryption is vital. Ensure that your data is encrypted both during transmission and while being stored in the cloud. This means that even if a hacker intercepts your data, they cannot read it without the decryption key.
- Regular Backups: No one is immune to data loss, whether due to accidental deletion, hardware failure, or cyber-attacks. Regularly backing up your data ensures that you can recover it in the event of a disaster, enabling business continuity and personal reassurance.
- Access Control: Limiting data access to only authorized personnel is crucial. Implement role-based access controls that assign permissions according to users’ needs. For instance, a marketing team might not require access to sensitive financial data, and restricting access can mitigate risks significantly.
By adopting these security practices, you not only protect your data but also enjoy peace of mind knowing that your information is better secured in the cloud. Given the rise in cyber threats observed year over year, especially in the United States with its tech-centric economy, staying informed and alert is imperative.
Exploring cloud storage applications that prioritize security features such as end-to-end encryption, compliance with industry standards, and robust customer support will equip you with the necessary tools to safeguard your data efficiently. As you delve deeper into enhancing your cloud security posture, remember that your proactive engagement is essential to navigate the evolving threat landscape effectively.
DISCOVER MORE: Click here to learn how A/B tests can enhance your app’s user experience

Essential Security Practices for Cloud Storage
In an era where digital information is an invaluable asset, the importance of implementing strict security practices for cloud storage applications cannot be overstated. Understanding and addressing the various risks associated with storing sensitive data in the cloud is paramount for both individuals and organizations. With the right strategies in place, users can significantly reduce their exposure to threats while leveraging the benefits of cloud technology.
1. Strong Password Hygiene
The cornerstone of securing your cloud storage begins with strong passwords. It is crucial to create passwords that are not easily guessed or compromised. Statistics indicate that over 80% of data breaches are linked to weak or stolen passwords, highlighting the need for heightened password hygiene. Consider employing the following guidelines to enhance your password security:
- Utilize a minimum of 12 characters, incorporating a combination of upper and lower-case letters, numbers, and special characters.
- Avoid using personal information or common phrases that can be easily associated with you.
- Regularly update your passwords and refrain from reusing them across multiple accounts.
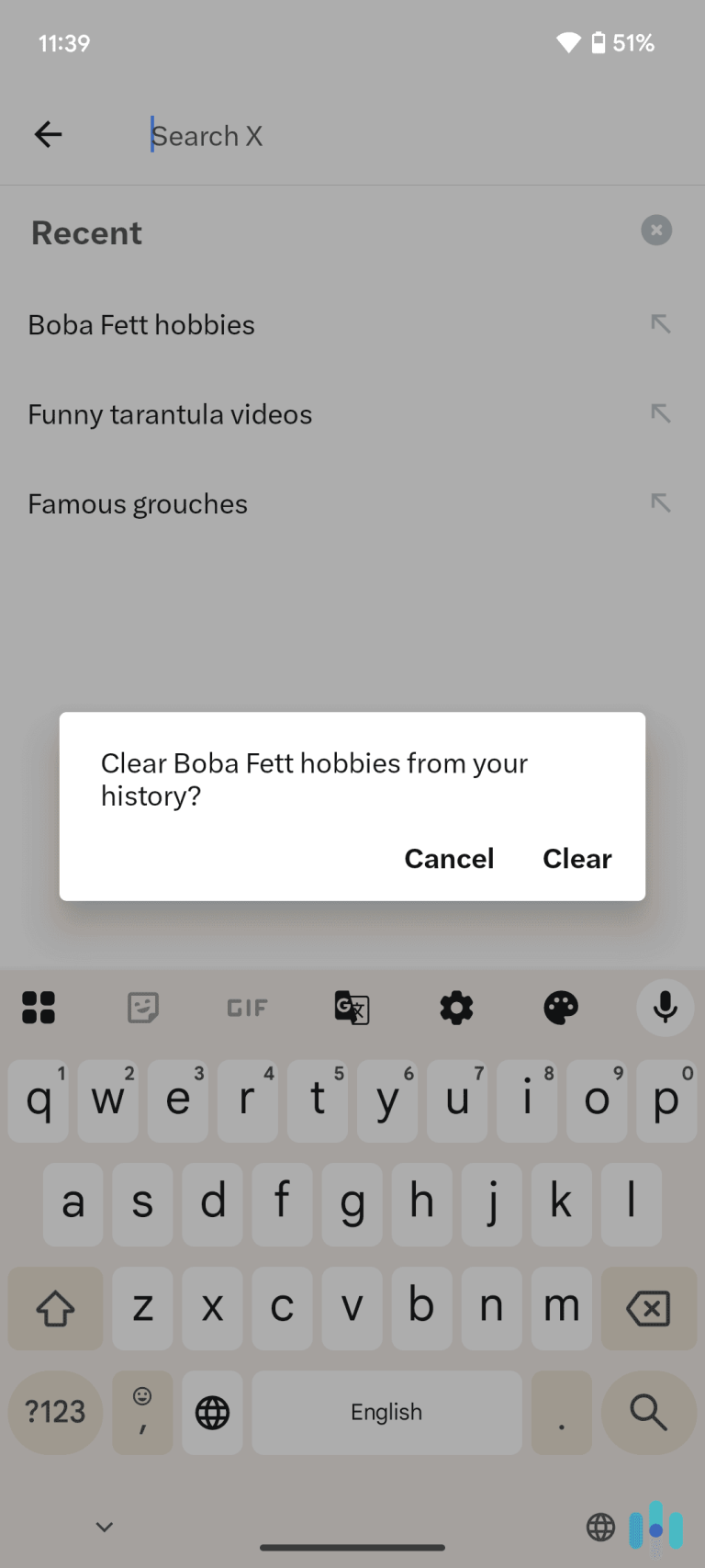
2. Enable Two-Factor Authentication (2FA)
Another highly effective measure is to enable two-factor authentication (2FA). This feature adds an extra layer of security by requiring two forms of verification before granting access to your account. Even if a hacker manages to acquire your password, they would still be unable to access your data without the second form of authentication, such as a temporary code sent to your mobile device or a biometric scan.
3. Leverage Data Encryption
Data encryption stands as a critical element in safeguarding your information. It involves converting your data into a coded format, rendering it unreadable without the proper decryption key. Implementing encryption both during transmission and storage in the cloud ensures that sensitive information remains confidential, even if intercepted. Prioritize cloud storage providers that offer end-to-end encryption to maintain data integrity.
4. Establish Regular Backup Protocols
Despite the inherent reliability of cloud services, no system is immune to failures, cyber-attacks, or human errors. Hence, establishing regular backups is essential to ensure data recovery and continuity in daily operations. Set up automated backups to a secure location, so in the event of an unforeseen incident, you can swiftly restore your data without significant loss.
5. Implement Access Control Measures
Access control is vital to mitigate risks associated with data exposure. By applying role-based access controls, you can restrict access to sensitive information according to the user’s role within the organization. This practice minimizes the potential for unauthorized individuals to interact with confidential data, thus enhancing overall security. Be sure to conduct regular audits of access permissions and modify them as necessary to adapt to any changes within your team.
By incorporating these essential security practices, you can significantly enhance the protection of your data in cloud storage applications. The evolving digital landscape necessitates a proactive approach to data security, empowering users to take charge of their information safety.
As cloud storage becomes an integral part of both personal and business operations, the significance of implementing effective security practices has grown tremendously. In a digital landscape rife with potential cybersecurity threats, understanding how to protect your data is essential for preserving its integrity and confidentiality. There are various strategies that can be employed to reinforce the security of your cloud-stored information.
One of the most fundamental practices is the use of strong passwords and employing multi-factor authentication (MFA). A strong password typically consists of a mix of letters, numbers, and special characters, making it difficult for unauthorized users to gain access. Coupling this with MFA adds an additional layer of security by requiring users to verify their identity through a secondary method, such as a text message or authentication app.
Encrypting your data while it is being uploaded to or stored in the cloud is another critical measure. Encryption protects sensitive information, rendering it unreadable without the appropriate decryption key. By ensuring that your files are encrypted, you greatly mitigate the risk of data breaches and unauthorized access.
Additionally, regular audits and monitoring of user activities can serve as a proactive approach to security. Implementing robust access controls allows you to determine who has permissions to view or edit sensitive documents. Regularly reviewing access logs may also help identify any unusual access patterns, highlighting potential threats before they escalate.
Lastly, ensuring that your cloud service provider complies with established standards and regulations is crucial. Look for service providers that adhere to industry best practices, as this not only enhances data security but also instills confidence in the governance of your data.
| Category | Key Features |
|---|---|
| Password Management | Use of complex passwords and MFA for enhanced security. |
| Data Encryption | Protecting data through encryption to prevent unauthorized access. |
| User Activity Monitoring | Conducting audits and monitoring user actions for potential threats. |
| Access Control | Implementing robust access controls to manage permissions. |
| Provider Compliance | Choosing providers that adhere to industry security standards. |
With these practices in place, users can significantly bolster their guarantees of safety against data loss and potential breaches. Staying informed and vigilant about best practices for cloud data security is key to ensuring that your information remains protected.
DISCOVER MORE: Click here to learn how A/B tests can enhance user experience
Advanced Security Considerations for Cloud Storage
As cloud storage solutions continue to evolve and integrate into our daily lives, users must be vigilant about the potential vulnerabilities that accompany this technology. Beyond the basic security measures previously discussed, there are additional strategies and practices that can enhance data protection in cloud environments. Understanding these advanced security measures allows users to stay ahead of threats and bolster the integrity of their information.
6. Monitor and Conduct Regular Security Audits
Regular security audits play a crucial role in revealing vulnerabilities and assessing the effectiveness of your security measures. By systematically reviewing your cloud storage configurations, access logs, and data management policies, organizations can identify and remediate potential weaknesses. Utilize available tools and services that specialize in threat detection and compliance monitoring tailored to your specific cloud environment. In fact, according to the Ponemon Institute, organizations that conduct regular audits experience 25% fewer security incidents, underscoring their importance in achieving robust data protection.
7. Stay Informed About Software Updates
Keeping software up to date is a fundamental security practice that many overlook. Cloud service providers frequently release updates to address vulnerabilities, reduce risks, and improve features. Ensure that you are utilizing the latest version of your cloud storage application, and enable automatic updates when available. Additionally, remain informed about any security advisories issued by your provider to understand the specific risks associated with older software versions.
8. Educate and Train Employees on Security Awareness
No security measure is foolproof without a well-informed user base. Employee training on security best practices is essential, particularly for organizations that handle sensitive data. Regularly conduct training sessions that cover topics such as phishing scams, data handling procedures, and the importance of strong authentication methods. A study by CybSafe indicates that employee awareness and training can reduce the likelihood of successful human-error-related breaches by up to 70%, evidencing that knowledge is as crucial as technology in data protection.
9. Utilize Virtual Private Networks (VPNs)
When accessing cloud storage services remotely, employing a Virtual Private Network (VPN) is an effective way to securely transmit information over the internet. A VPN encrypts your internet connection, making it significantly more difficult for hackers to intercept data. This is particularly important for individuals working from home or using public Wi-Fi networks, where exposure to cyber threats is heightened. By utilizing a reliable VPN service, users can ensure that their sensitive information remains confidential, even in less secure environments.
10. Understand Compliance and Regulatory Requirements
Depending on the nature of your data, adhering to compliance and regulatory mandates is paramount. Regulations such as the Health Insurance Portability and Accountability Act (HIPAA) for healthcare, the General Data Protection Regulation (GDPR) in Europe, and the California Consumer Privacy Act (CCPA) govern how personal information should be handled and stored. Familiarizing yourself with these regulations and ensuring your cloud storage provider complies can mitigate the risk of legal repercussions and enhance your organization’s credibility among clients and partners.
As the landscape of cloud storage continues to grow more intricate, it is imperative to stay attuned to the latest security practices. By adopting a multi-layered approach that includes user education, technology updates, and strong regulatory compliance, individuals and organizations alike can fortify their defenses against potential data breaches.
DIVE DEEPER: Click here to uncover insights
Conclusion: Fortifying Your Data in Cloud Storage
In an era where data breaches are increasingly commonplace, understanding and implementing robust security practices for cloud storage applications is essential. As highlighted throughout this article, adopting a comprehensive approach that includes regular audits, staying updated on software releases, and conducting employee training can significantly reduce vulnerabilities and enhance protection. Furthermore, leveraging technologies like Virtual Private Networks (VPNs) helps safeguard sensitive information during remote access, while knowledge of compliance requirements ensures that organizations maintain integrity and avoid legal repercussions.
As digital landscapes evolve, so too must our defenses against evolving threats. By prioritizing security measures and cultivating an informed user base, individuals and organizations can create a stronger line of defense against potential cyber risks. Imagine the confidence of sharing critical data, knowing you have implemented comprehensive security strategies. This proactive stance towards securing cloud data not only protects sensitive information but also builds trust with clients and stakeholders.
While it may seem daunting, enhancing your cloud storage security practices is an ongoing journey rather than a one-time task. For those looking for deeper insights into emerging trends and technologies in cloud security, continued education and engagement with security professionals can provide valuable resources. The responsibility of protecting your data ultimately lies in your hands—take charge and fortify your digital assets today for a safer tomorrow.
Related posts:
Safety Tips for Using Cloud Storage Applications
Tips for Enabling Two-Factor Authentication in Your Favorite Apps
Tips to Enhance the Security of Your Financial Transactions in Payment Apps
How to Choose Apps with Transparent and Secure Privacy Policies
How to Protect Your Mobile Devices from Malware in Apps
Strategies for Secure Password Management in Various Applications
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.