Cryptography Techniques to Enhance the Security of Your Files in Applications
The Importance of Cryptography in Data Protection
In a world where personal and organizational data is frequently exchanged over the internet, the importance of cryptography techniques has never been more pronounced. From financial transactions to private communications, safeguarding these files against potential breaches is essential. Data breaches can lead to devastating consequences, including identity theft and financial loss, underscoring the necessity of effective security measures.
Underpinning modern security practices are several fundamental cryptography techniques that serve various purposes in protecting sensitive data. By utilizing these methods, individuals and organizations can enhance their defenses against potential threats.
Symmetric Encryption
Symmetric encryption is one of the foundational techniques used for data protection, relying on a single key for both the encryption and decryption processes. This method is particularly advantageous when dealing with large volumes of data due to its speed and efficiency. For example, the Advanced Encryption Standard (AES) is widely employed in government and private sectors alike to encrypt everything from emails to secure network communications.
The efficiency of symmetric encryption can dramatically reduce the time required to protect critical files. However, the major downside lies in the management of the encryption keys; if the key is compromised, unauthorized parties can easily decrypt the data. This vulnerability necessitates careful key management and secure transmission practices.
Asymmetric Encryption
In contrast, asymmetric encryption employs a dual-key approach that includes a public key for encryption and a private key for decryption. This method adds an essential layer of security, especially for sensitive transactions such as online banking or secure communications. For instance, platforms like Signal and WhatsApp utilize asymmetric encryption to secure messages, allowing users to communicate privately without fear of interception.
One major advantage of asymmetric encryption is that it negates the need to exchange private keys, which significantly reduces the potential for key theft. However, asymmetric encryption is generally slower than symmetric encryption, making it less suitable for encrypting large files.
Hash Functions
Another vital component in the realm of data protection is the use of hash functions. These algorithms take input data and produce a fixed-size string of characters, known as a hash. Hash functions are integral in ensuring data integrity by allowing users to verify whether a file has been altered. For example, many software installations and downloads utilize hash functions to confirm that files remain uncorrupted during transfer.
Moreover, hash functions can be paired with digital signatures to authenticate the source of a message or file, further enhancing security. Technologies such as Secure Hash Algorithm (SHA) are commonly used for this purpose, ensuring that any unauthorized alterations are easily detectable.
Building Trust Through Robust Security
Implementing these cryptography techniques not only safeguards sensitive information but also fosters trust with users and clients alike. As reliance on digital applications grows exponentially, understanding and utilizing these cryptography techniques becomes imperative for both individuals and organizations.
Ultimately, navigating the complexities of data protection becomes less daunting with a solid grounding in these methodologies. By equipping yourself with this knowledge and employing these techniques, you are taking proactive steps toward enhancing your file security and ensuring a safer digital landscape for everyone.
DISCOVER MORE: Click here to learn how A/B tests can enhance your app’s user experience
Understanding Key Cryptography Methods for File Security
In the digital age, where data breaches are alarmingly common, understanding the fundamental cryptography techniques is essential for maintaining the integrity and confidentiality of sensitive files. These methods not only protect against unauthorized access but also play a crucial role in ensuring that data remains secure during transfer and storage. Below, we delve into various cryptography practices that individuals and organizations can employ to enhance the security of their files in applications.
Hybrid Encryption
Hybrid encryption combines the strengths of both symmetric and asymmetric encryption methods, providing a more robust security solution. In this approach, asymmetric encryption is used to securely exchange a symmetric key, which then encrypts the actual data. This technique leverages the speed of symmetric encryption while maintaining the secure exchange of keys typical of asymmetric methods. Many secure communication protocols, including Transport Layer Security (TLS), utilize hybrid encryption to protect sensitive transactions over the internet.
The benefits of hybrid encryption include:
- Increased security: By mixing both encryption methods, hybrid encryption reduces the risk of key exposure.
- Efficiency: It maintains high-speed data encryption while ensuring secure key management.
- Scalability: Suitable for varying data sizes and types, making it versatile for different applications.
Public Key Infrastructure (PKI)
Public Key Infrastructure (PKI) provides a framework for managing digital certificates and public-key encryption. It establishes a secure method for users to exchange data and verify the identity of parties involved in a transaction. PKI enables processes like secure email (PGP), SSL certificates for secure websites, and digital signatures.
The key components of PKI include:
- Certificate Authority (CA): The trusted entity responsible for issuing and managing digital certificates.
- Registration Authority (RA): Responsible for accepting requests for digital certificates and authenticating the entity making the request.
- Digital Certificates: Documents that bind a public key to the identity of an individual or organization, used to establish trust.
One of the main advantages of PKI is its ability to prevent man-in-the-middle attacks where an unauthorized party could intercept communications. By verifying the identities involved in data exchange, PKI significantly boosts the overall security of file transfers and communications.
Digital Certificates and Signing
Digital certificates are essential for authenticating the identity of users and ensuring secure communications. When files are digitally signed using a certificate, the recipient can trust that the file originated from the claimed sender and has not been altered in any way. This process is invaluable for businesses that need to confirm the legitimacy of documents, such as contracts or financial statements, before processing them.
Utilizing digital signatures can provide multiple advantages:
- Data integrity: Ensures that the content of the file has not been tampered with.
- Non-repudiation: The sender cannot deny sending the document, providing legal protection.
- Trust establishment: Fosters trust between parties, as the signature validates the source of the information.
As the digital landscape evolves, employing these cryptography techniques becomes imperative. They not only act as a defense against attacks but also build a foundation of trust in electronic transactions. By exploring and implementing these methods, you can significantly enhance the security of your files in applications, fostering a safer digital environment for all.
Cryptography Techniques to Enhance the Security of Your Files in Applications
Welcome to the world of cryptography, where the integrity and security of sensitive data are fortified through sophisticated algorithms and protocols. In an era where cyber threats are increasingly rampant, understanding these techniques is imperative for businesses and individuals alike. Encrypting files not only protects confidential information but also enhances trust between clients and providers.
Among the most promising techniques are Symmetric Key Encryption and Asymmetric Key Encryption. Symmetric encryption employs a single key for both encryption and decryption, making it a fast and efficient method for encrypting substantial amounts of data. In contrast, asymmetric encryption uses a pair of keys—a public key for encryption and a private key for decryption—which ensures a higher level of security, especially in peer-to-peer communication scenarios.
Additionally, Hash Functions play a crucial role in data integrity. By converting an input into a fixed-size string of characters, hash functions help verify data authenticity without exposing it. They are essential in scenarios where you need to ensure that files have not been altered during transmission.
Integrating these cryptography techniques within applications can significantly mitigate the risks of unauthorized access and data breaches. Moreover, ongoing advancements in cryptographic methods, such as quantum cryptography, promise even greater security landscapes in the future.
| Category | Key Features |
|---|---|
| Symmetric Key Encryption | Uses a shared secret key for fast encryption and decryption, ideal for large data sets. |
| Asymmetric Key Encryption | Utilizes a pair of keys for enhanced security in communication and data exchange. |
| Hash Functions | Ensures data integrity by verifying that files remain unchanged across transitions. |
| Quantum Cryptography | Offers potential security against future quantum computing threats with advanced protocols. |
Understanding and applying these cryptographic techniques is essential for anyone looking to safeguard their files and maintain secure applications. By proactively adopting these technologies, users can significantly enhance the security landscape and ensure that their sensitive information is well-protected against potential threats.
DISCOVER MORE: Click here to learn how A/B tests can enhance user experience
Advanced Cryptographic Techniques for Enhanced File Security
As cyber threats evolve and become increasingly sophisticated, employing more advanced cryptographic techniques becomes essential for safeguarding vital data. There are several contemporary methods that not only bolster file security but also streamline processes in applications. By familiarizing yourself with these advanced techniques, you can significantly improve your approach to file security.
Homomorphic Encryption
Homomorphic encryption stands out as a cutting-edge technique that allows computation to be performed on encrypted data without requiring decryption. This means sensitive information can remain secure even when being used for calculations or analytical purposes. The implications of homomorphic encryption are vast, particularly in sectors like healthcare and finance, where privacy is paramount.
The benefits of homomorphic encryption include:
- Data privacy: Users can perform operations on encrypted data, ensuring that sensitive information never leaves the encrypted state.
- Utility in cloud computing: Users can leverage cloud services without exposing their data, maintaining confidentiality while still using external processing capabilities.
- Enhanced security: Attacks targeting raw data become less effective because the data remains encrypted throughout the entire process.
Access Control and Encryption Policies
Access control mechanisms coupled with well-defined encryption policies are vital for governing who can access and manipulate sensitive files. These policies dictate how data will be handled, encrypted, and decrypted, ensuring it is only accessible to authorized users.
Implementing robust access control measures involves:
- Role-based access: Assigning permissions based on user roles within an organization, limiting access to files strictly according to job functions.
- Least privilege principle: Users are given the minimum level of access necessary for their tasks, reducing the risk of unauthorized data exposure.
- Audit trails: Maintaining logs of who accessed what data and when, providing transparency and accountability.
Combining access control measures with strong encryption practices creates a multi-layered defense strategy, making it significantly more difficult for unauthorized individuals to gain access to sensitive files.
Blockchain Technology
Blockchain technology is not just for cryptocurrencies; it can also enhance file security through decentralized storage and assurance of data integrity. With its intrinsic properties of immutability and transparency, blockchain secures files against unauthorized alterations, making it highly attractive for data-sensitive industries like banking and legal services.
Key advantages of using blockchain for file security include:
- Decentralization: Data is distributed across many nodes, reducing the risk of centralized data breaches.
- Immutability: Once data is recorded on the blockchain, it cannot be altered without consensus from the network, providing a permanent and verifiable record.
- Smart contracts: Allow predefined agreements to be executed automatically when conditions are met, enhancing operational efficiency without sacrificing security.
Zero-Knowledge Proofs
Zero-knowledge proofs (ZKPs) enable a party to prove to another that they know a value without revealing the actual value itself. This intriguing concept enhances security in a variety of applications, especially in scenarios where data privacy is non-negotiable, such as identity verification and confidential transactions.
Implementing zero-knowledge proofs offers the following benefits:
- Privacy protection: Sensitive data is not disclosed during the verification process, minimizing exposure to potential threats.
- Easier compliance: Organizations can comply with data protection regulations without needing to store customer-sensitive information.
- Enhanced trust: By proving knowledge without revealing actual data, ZKPs build confidence in secure transactions and interactions.
By investing time to understand and implement these advanced cryptographic techniques, individuals and businesses can create robust defenses for their files within applications. The interplay of evolving cryptographic practices provides a strategic advantage in the ongoing battle against digital threats, promising a more secure future for sensitive data handling.
DISCOVER MORE: Click here to enhance your understanding
Conclusion: Elevating File Security through Reliable Cryptography
In a world where data breaches and cyber threats are increasingly prevalent, understanding and implementing cryptography techniques is no longer optional but essential for anyone managing sensitive information. From the revolutionary capabilities of homomorphic encryption that allows computation on encrypted files, to blockchain technology offering secure, immutable records, each technique presents a unique method to fortify your file security protocols. Furthermore, integrating sophisticated access control measures and encryption policies can ensure that only authorized personnel have the ability to manipulate data, safeguarding it against insider threats.
Moreover, advancements such as zero-knowledge proofs offer an intriguing balance between privacy and verification, reinforcing trust in transactions while minimizing exposure to risks. As organizations, particularly in the United States, face stringent data regulations, these techniques enable compliance without compromising user data integrity. Adopting a multi-layered security approach that incorporates these cutting-edge cryptographic methods empowers businesses to combat evolving digital threats effectively.
Ultimately, exploring these options not only enhances the security of files in applications but also promotes an environment of confidence and trust among users. As the digital landscape continues to evolve, staying informed and proactive about cryptographic innovations will prove to be invaluable in ensuring the protection of your data. Dive deeper into these methods, as their impact could very well shape the future of data security in your organization.
Related posts:
Security in Finance Apps: How to Protect Your Transactions and Banking Information
How to Protect Your Mobile Devices from Malware in Apps
How to Protect Your Personal Data on Social Media Apps
How to Protect Your Personal Data on Social Media Apps
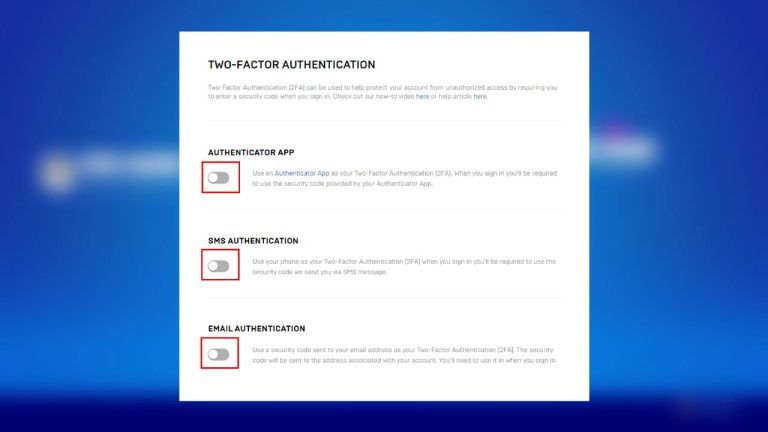
The Importance of Two-Factor Authentication in Popular Apps
How to Protect Your Data in Health and Wellness Apps
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.