Best Practices for Managing Mobile Devices in Corporate Environments
Impact of Mobile Devices on Corporate Operations
In today’s dynamic business environment, mobile devices are more than just communication tools; they have transformed into integral components that streamline processes and enhance productivity. As workforce mobility increases, organizations have recognized the necessity of optimizing mobile technology to foster seamless workflows. However, this rapid integration presents intricate challenges requiring careful navigation.
To effectively leverage mobile devices while mitigating risks, companies must prioritize the implementation of best practices for managing mobile devices. These practices serve as guidelines to create a secure and productive workspace. Here are several pivotal considerations:
- Security Protocols: Establishing robust security measures is essential. This includes implementing encryption technologies, which protect sensitive data during transmission, and instituting secure access controls that limit who can access certain information on mobile devices. For instance, using multifactor authentication (MFA) can drastically enhance security by requiring users to provide two or more verification factors to gain access.
- Policy Development: Creating a comprehensive mobile device policy can greatly influence how employees use their devices in a corporate setting. This policy should delineate allowable uses, outline responsibilities, and specify consequences for violations. Engaging employees in policy formulation can also ensure buy-in and compliance, thus promoting a culture of security.
- Training: Regular training sessions can empower employees to recognize potential risks associated with mobile technology. These sessions could include practical demonstrations on identifying phishing attempts or managing sensitive corporate information. Such educational programs can reduce the likelihood of human error, a significant factor in security breaches.
Emerging Trends and Strategies
As mobile devices continue to evolve, businesses should remain vigilant regarding emerging trends that may impact device management. One substantial trend is the BYOD (Bring Your Own Device) policy, which allows employees to use their personal devices for work purposes. While this practice can enhance flexibility and satisfaction among workers, it requires precise guidelines to ensure organizational safety and compliance.
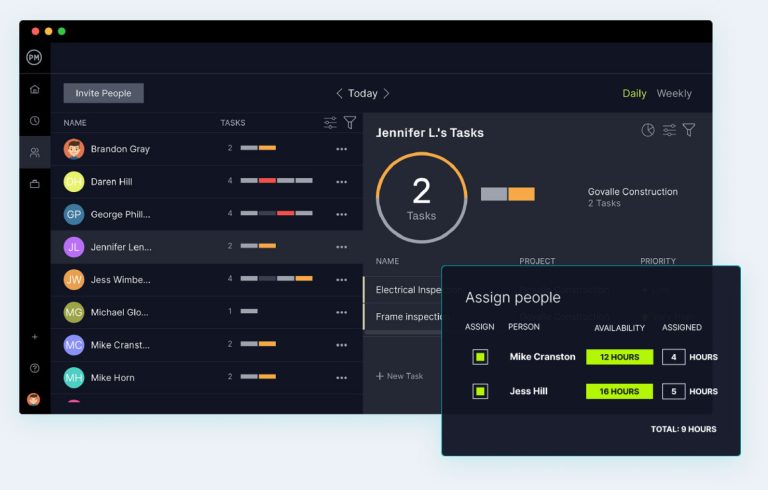
Furthermore, employing Mobile Device Management (MDM) tools enables organizations to monitor and control the security of devices remotely. MDM can facilitate the management of software updates, application installations, and device wipe processes if a device is lost or stolen. This control ensures that corporate data remains protected even in the event of device loss.
Additionally, regular updates to software and security systems are critical in addressing newly discovered vulnerabilities. Companies should implement automatic updates whenever possible to ensure that all devices are running the latest, most secure versions of software. This proactive approach is crucial in a landscape where cyber threats are increasingly sophisticated.

By adopting and adhering to these best practices, organizations can not only harness the full potential of mobile technology but also fortify their defenses against potential data breaches and disruptions. An informed approach to mobile device management enhances overall organizational resilience and supports a secure and efficient corporate environment. As companies increasingly rely on mobile technology, a strategic and forward-thinking perspective will become indispensable in navigating the complexities of this evolving landscape.
DON’T MISS: Click here to discover how A/B tests can enhance user experience
Key Considerations for Effective Mobile Device Management
In the quest to leverage mobile technology within corporate environments, it becomes imperative to understand the fundamentals of effective mobile device management (MDM). As businesses increasingly adopt mobile devices to foster communication and productivity, the need for well-defined strategies to manage them effectively is paramount. The following considerations are pivotal in ensuring a secure and optimized mobile framework:
- Device Inventory: Maintaining a comprehensive inventory of all mobile devices used within the organization is crucial. This allows for better tracking of devices, monitoring their usage, and managing software installations. By having a clear picture of the devices in circulation, companies can prevent unauthorized access and ensure that all devices adhere to corporate policies.
- Compliance Management: With strict regulations such as GDPR and HIPAA in place, organizations must ensure that their mobile device policies comply with legal standards. Incorporating compliance checks into the MDM framework can help organizations avoid costly fines and reputational damage. Regular audits of mobile devices can pinpoint compliance gaps and allow for timely adjustments.
- Employee Input: Engaging employees in the decision-making process regarding mobile device policies fosters a sense of ownership and responsibility. By soliciting their feedback on the usability and functionality of mobile technology, businesses can create more effective policies that align with employee needs while enhancing corporate security measures.
Moreover, organizations should consider the implications of emerging technologies on mobile device management. With the advent of cloud computing and mobile applications, it is crucial to establish guidelines around acceptable app usage and data storage practices. By paving the way for secure mobile application development and deployment, businesses can enhance their operational efficiency without sacrificing security.
Addressing Security Risks and Developing Contingency Plans
The ubiquitous nature of mobile devices introduces various security risks that organizations must address proactively. Implementing a risk assessment strategy can help identify vulnerabilities and prioritize resources accordingly. Security gaps often stem from unauthorized applications, poor password practices, or even employee negligence. Organizations should continuously monitor these threats to develop robust defenses.
Creating a well-documented incident response plan is also critical in addressing potential security breaches effectively. This plan should outline specific actions to be taken in the event of a data breach or device compromise, ensuring that employees know who to contact and what steps to follow. Regularly rehearsing these protocols can prepare employees for real incidents, minimizing panic and confusion.
In conclusion, navigating the complexities of mobile device management within corporate environments requires a multifaceted approach. By recognizing the importance of device inventory, compliance management, employee input, security risk assessment, and incident response planning, organizations can significantly enhance their operational security and productivity. As mobile technology continues to evolve, adopting these best practices will prepare companies not only to defend against threats but also to seize opportunities for innovation and growth.
| Security Protocols | Importance |
|---|---|
| Regular Software Updates | Maintaining the latest software ensures the protection against vulnerabilities. |
| Strong Password Policies | Implementing complex password requirements significantly reduces unauthorized access. |
| Device Encryption | Encrypting data protects sensitive corporate information from potential breaches. |
| Remote Wipe Capabilities | Allows for quick data removal in case devices are lost or stolen, maintaining corporate data integrity. |
Incorporating these security protocols is crucial when developing a strategy for managing mobile devices effectively in corporate environments. Regular software updates not only enhance performance but also safeguard against newly identified threats, ensuring the organization remains secure against cyber risks. Furthermore, enforcing strong password policies is essential; complex passwords serve as the first line of defense, making it harder for unauthorized individuals to breach security measures.Moreover, implementing device encryption protects sensitive corporate information, ensuring that data remains inaccessible even if the device is compromised. Additionally, remote wipe capabilities provide a rapid response to potential data breaches, allowing IT departments to erase sensitive information if a device is lost or stolen. Together, these practices create a robust framework for mobile device management, reinforcing the security posture of the organization.
DISCOVER MORE: Click here to enhance your app’s user experience
Implementing Robust Policies and Employee Training
As organizations navigate the intricate landscape of mobile device management (MDM), establishing clear policies is fundamental to ensuring security and compliance. Organizations must develop formalized guidelines for mobile device usage that encompass everything from acceptable use policies to consequences for violations. These policies should clearly define whether employees are allowed to use personal devices for work purposes (commonly referred to as Bring Your Own Device or BYOD) or if the company will provide dedicated devices. By articulating these parameters, companies can reduce risks stemming from device misuse and mismanagement.
Furthermore, integrating employee training programs is a vital component of an efficient MDM strategy. A well-informed workforce is key to maintaining security and compliance standards. Training sessions can include topics such as password management, recognizing phishing attempts, and understanding the implications of data leaks. Regular refresher courses should also be conducted to reinforce knowledge and adapt to new security threats. According to a 2021 report from a prominent cybersecurity firm, more than 90% of security breaches stem from human error, underscoring the critical need for constant education and vigilance.
The Role of Mobile Device Management Solutions
To ensure effective mobile device management, organizations should explore comprehensive MDM solutions. These platforms allow IT teams to manage and secure mobile devices remotely. A good MDM solution enables functionalities such as remote wipe of lost or stolen devices, application whitelisting, and enforcement of security policies. According to a study by MarketsandMarkets, the global MDM market is projected to reach $10.9 billion by 2026, highlighting its growing importance in corporate settings.
Additionally, organizations should prioritize data encryption and security updates on all devices. Encryption ensures that sensitive corporate data is unreadable without proper access credentials, adding a necessary layer of protection in the event of device theft. Keeping software updated is equally critical; outdated applications can have vulnerabilities that cybercriminals may exploit. Organizations must instill a culture that recognizes the importance of timely updates as part of their MDM strategy.
Monitoring and Analyzing Device Performance
Once policies are in place and MDM solutions are implemented, organizations must participate in ongoing monitoring and analysis of mobile device performance. Analyzing device usage and security incidents provides valuable insights into the effectiveness of existing policies and can reveal areas for improvement. For example, frequent app crashes or connectivity issues may indicate that employees are using unauthorized applications that impact performance negatively. By harnessing analytics, companies can refine their mobile strategies based on real data.
Moreover, adopting a framework for continuous improvement in mobile device management is essential. Regularly soliciting feedback from employees on their experiences with mobile devices can unveil underlying problems and lead to enhanced engagement. Through surveys and focus group discussions, organizations can gather vital information that supports better decision-making and policy adjustments.
In the fast-paced world of mobile technology, the ability to adapt swiftly and effectively to both emerging trends and security vulnerabilities will give organizations the competitive edge they need. By embracing best practices for managing mobile devices, companies can fortify their defenses, maintain compliance, and foster a productive work environment.
DISCOVER MORE: Click here to delve deeper
Conclusion: Elevating Mobile Device Management in the Corporate Landscape
In today’s digital age, the effective management of mobile devices within corporate environments cannot be overstated. As we have explored throughout this article, implementing a comprehensive strategy that includes clear policies, robust training programs, and reliable MDM solutions is key to safeguarding sensitive information while enhancing productivity. Organizations must recognize that the integration of mobile technology into their operations comes with significant responsibilities—most notably the necessity to protect corporate data against relentless cyber threats.
Prioritizing data encryption and regular security updates ensures that valuable information remains secure, while continuous monitoring and analytics allow businesses to adapt quickly to potential vulnerabilities. Furthermore, fostering a culture of security awareness through ongoing education empowers employees to act as the first line of defense against data breaches, making them instrumental in any effective mobile strategy.
As new technologies emerge, organizations should remain vigilant and adaptable, continuously evaluating their practices and investing in the latest MDM technologies. The importance of engaging staff in this process through feedback and collaborative discussions not only strengthens the mobile management framework but also cultivates a sense of shared responsibility for security.
Ultimately, integrating these best practices for managing mobile devices can serve as a catalyst for innovation and efficiency. Companies that take decisive steps in refining their mobile strategies will not only enhance their operational performance but also position themselves as industry leaders in a landscape that is increasingly defined by mobility.
Related posts:
Device Management in Educational Environments: Tools and Strategies
How to Choose the Ideal Device Management Platform for Your Business
How to Implement Device Management Policies in Regulated Sectors
Device Management and Sustainability: Strategies to Reduce Environmental Impact
IoT Device Management: Challenges and Innovative Solutions
Impact of 5G on Device Management and Connectivity
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.