How to Implement Device Management Policies in Regulated Sectors
The Crucial Role of Device Management Policies in Modern Organizations
In an era characterized by rapid technological advancement, the implementation of robust device management policies has become essential, especially in highly regulated industries. For example, sectors such as healthcare, finance, and government not only grapple with a myriad of technological challenges but also face stringent compliance requirements that demand an unwavering commitment to data protection and operational integrity. The stakes are especially high, as any lapses can result in severe consequences, including substantial fines and loss of reputation.
A well-crafted device management policy offers a structured approach to managing organizational devices effectively, thus streamlining operations while enhancing security measures. To appreciate the significance of such policies, it’s crucial to explore key aspects that define their effectiveness:
- Data Security: The foremost concern for most organizations is protecting sensitive information from data breaches, which can happen through various avenues, including lost devices or unauthorized software installations. Implementing encryption protocols, multifactor authentication, and continual monitoring can safeguard against breaches, thereby protecting customer data and maintaining trust.
- Compliance: Organizations must navigate a complex web of industry standards such as HIPAA in healthcare, which mandates strict rules around patient information privacy, and FINRA in finance, which governs data handling practices. Noncompliance can lead to hefty fines or even the revocation of the ability to operate. By adhering to these regulations, organizations can ensure legal and operational viability.
- Device Inventory: A comprehensive inventory of all devices in use is vital for effective device management. This practice not only aids in tracking hardware assets but also helps in identifying those devices that may be vulnerable to security threats. Regular audits can mitigate risks associated with outdated or unsupported devices, ensuring that every entry in the inventory is secure and compliant with the established policies.
As organizations devise and implement these policies, it is equally important to focus on understanding available technology alongside the regulatory landscape. This dual focus requires organizations to create rules that are not only comprehensive but also adaptable to technological changes. Additionally, education plays a pivotal role; training staff across all levels encourages adherence to policies and fosters a culture of security awareness.
Ultimately, a well-designed device management policy can shield an organization from the risks associated with non-compliance and data breaches. It encourages vigilance, promotes security best practices, and lays the foundation for operational excellence. Thus, understanding and implementing these policies effectively is not merely a checkbox on a compliance list but a vital step toward safeguarding an organization’s future in an increasingly digital world.
DISCOVER MORE: Click here to learn how A/B tests can enhance your app’s user experience

Understanding the Key Components of Effective Device Management Policies
Implementing device management policies in regulated sectors is not merely a procedural exercise; it requires a meticulous approach that aligns with both organizational goals and regulatory obligations. This process can be broken down into several critical components that organizations must prioritize to build a solid framework for device management.
1. Establishing Clear Objectives
Before diving into the technical aspects of device management, organizations must first define clear objectives. What are the specific regulatory requirements that need to be met? Is the goal to bolster data security, enhance compliance, or streamline operational efficiency? Setting measurable goals allows organizations to tailor their policies according to the unique challenges posed by their industry landscape, ensuring compliance with regulations such as HIPAA for healthcare organizations or GDPR for those handling data in the European Union.
2. Developing a Risk Management Strategy
A critical part of any device management policy is the risk management strategy. This involves identifying potential risks related to device usage and network access. For instance, organizations should assess which devices are most vulnerable to attacks and develop mitigation plans accordingly. Such plans might include regular updates and patches for software, establishing fail-safes for data breaches, and implementing strict access controls to sensitive information. By proactively managing these risks, organizations can lower their chances of encountering significant data incidents and the resultant financial ramifications.
3. Implementing Robust Access Controls
Access controls are a cornerstone of device management policies, especially in regulated environments. These controls dictate who can access what information and under what circumstances. Businesses should implement role-based access control (RBAC), ensuring that employees have access solely to the data necessary for their job functions. By doing this, organizations can minimize the risk of unauthorized access and protect sensitive information from both external and internal threats.
4. Continuous Monitoring and Evaluation
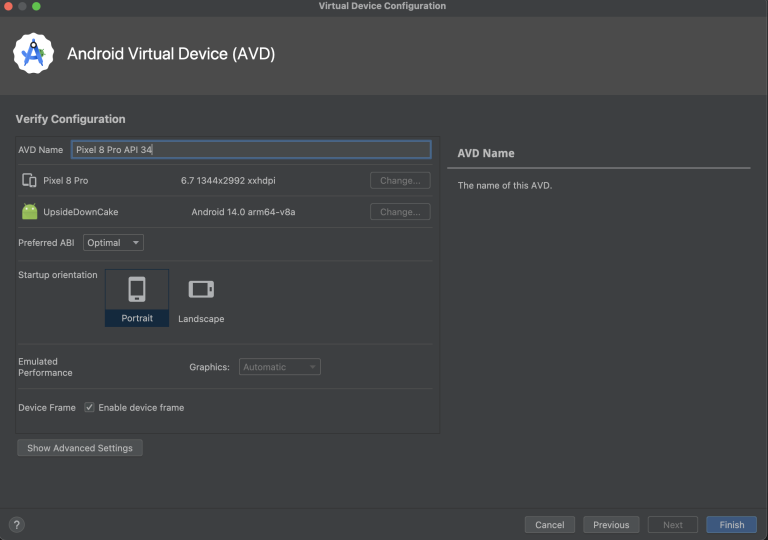
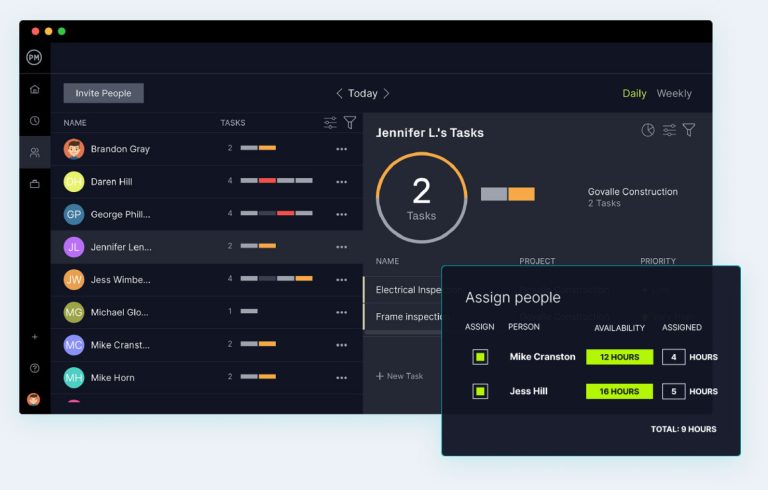
Once device management policies are in place, ongoing monitoring and evaluation are key to maintaining their effectiveness. Using tools such as mobile device management (MDM) or unified endpoint management (UEM) can allow organizations to constantly track device compliance, monitor for anomalies, and ensure that all devices are operating under the guidelines set forth in their policies. Regular audits can further enhance this process, providing a systematic approach to identifying potential weaknesses or outdated policies that may require immediate updates.
5. Fostering a Culture of Compliance
No policy is effective without the commitment of the organization’s personnel. It is essential to foster a culture of compliance that emphasizes the importance of adhering to device management policies. Regular training sessions and updates on best practices can empower employees to take ownership of their role in maintaining security. By embedding compliance into the organizational ethos, companies can greatly enhance their resilience against cyber threats and regulatory breaches.
In summary, implementing device management policies in regulated sectors involves more than just setting rules; it requires an integrated approach that incorporates risk assessment, access control, continuous monitoring, and most importantly, employee engagement. By addressing these key components, organizations can not only comply with regulatory requirements but also position themselves for sustainable success in the digitally-driven economy.
| Advantage | Description |
|---|---|
| Compliance Assurance | Effective device management policies ensure that organizations in regulated sectors consistently meet legal and regulatory standards. |
| Data Security Enhancement | Implementing these policies helps in proactively safeguarding sensitive information from unauthorized access and potential breaches. |
| Operational Efficiency | Streamlined processes for managing devices reduce operational risks and improve overall productivity by minimizing downtime. |
| User Accountability | Clear policies foster a culture of responsibility among users, ensuring everyone understands their roles in maintaining security. |
A well-structured device management policy is vital for organizations operating within regulated environments. It ensures regulatory compliance by defining protocols that adhere to industry standards. These policies substantially enhance the security of sensitive data, forming a protective barrier against illicit access and data breaches. The implementation of such policies can lead to increased operational efficiency as teams manage devices better, reducing the likelihood of disruptions and boosting productivity. Furthermore, fostering user accountability through clear guidelines establishes a collective responsibility in maintaining device security, reinforcing a secure culture within the organization.By exploring these benefits, organizations can turn compliance challenges into opportunities for growth and security enhancement, paving the way for a more secure and efficient operational framework.
DISCOVER MORE: Click here to learn how A/B tests can enhance your app’s user experience
Integrating Technology and Processes for Effective Device Management
As organizations in regulated sectors embark on the journey of implementing device management policies, the intersection of technology and structured processes becomes paramount. Leveraging sophisticated tools and applying a holistic approach can enhance compliance and security, while simultaneously refining operational efficiency.
6. Utilizing Advanced Technology Solutions
In the fast-evolving landscape of cybersecurity, utilizing advanced technology solutions is essential for effective device management. Enterprises should consider investing in technologies such as Artificial Intelligence (AI) and Machine Learning (ML) that can enhance threat detection and response times. For instance, AI-powered solutions can analyze patterns of behavior across devices and swiftly identify any anomalies indicative of a security breach. This proactive approach not only helps in adhering to regulations but also helps in preventing data incidents that could lead to penalties or reputational damage.
7. Automating Policy Enforcement
To ensure policies are consistently enforced, organizations should look into automation tools that reduce human error and improve compliance rates. Automation can facilitate the deployment of security patches across devices, ensuring all endpoints are safeguarded against known vulnerabilities. Additionally, automating compliance checks can provide real-time insights into which devices may not be adhering to established regulations, enabling swift corrective actions. According to a 2022 report by the Ponemon Institute, organizations that utilize automation in their compliance efforts can reduce the time spent on audits by up to 30%, significantly enhancing operational efficiency.
8. Creating Incident Response and Recovery Plans
An effective incident response and recovery plan is a critical element of device management, particularly in regulated sectors where data breaches can have severe repercussions. Organizations must outline clear protocols that detail immediate actions to take upon discovering a data breach, including incident notification procedures, forensic analysis, and communication strategies. Establishing a response team trained in crisis management can further solidify an organization’s resilience against potential threats. Case studies, such as the Target data breach of 2013, highlight the importance of having a robust incident response plan, as the lack of such a framework contributed significantly to the fallout of the incident.
9. Collaborating with Regulatory Bodies and Industry Experts
Engaging with regulatory bodies and industry experts can provide organizations with valuable insights into compliance trends and best practices. By fostering relationships with regulatory entities, organizations can gain a better understanding of evolving compliance requirements and anticipate changes that may impact their device management practices. Participating in industry forums and attending compliance workshops can also equip organizations with the latest knowledge and networking opportunities with peers who face similar challenges. A proactive approach to collaboration can not only help organizations remain compliant but also position them as leaders in the industry.
10. Regular Policy Review and Adaptation
Lastly, device management policies should not be static; they require regular review and adaptation to remain effective in a dynamic regulatory environment. Organizations must implement a schedule for reviewing policies, taking into account both technological advancements and changes in regulations. By fostering a feedback loop—where employees can report on the policy effectiveness based on their experiences—organizations can continuously refine their device management strategies. This iterative process ensures that the policies not only comply with current regulations but also adapt to evolving threats.
Incorporating these elements into device management policies can streamline compliance and security in regulated sectors. By integrating technology, automating processes, and remaining flexible to change, organizations stand to improve both their regulatory adherence and overall operational integrity, positioning themselves favorably in an increasingly complex digital world.
DISCOVER MORE: Click here to learn how A/B tests can enhance user experience
Conclusion: Paving the Way for Secure Device Management
In the evolving landscape of regulated sectors, the implementation of device management policies is not merely a compliance checkbox—it is a linchpin for safeguarding sensitive data and ensuring operational integrity. Organizations must understand that the successful integration of technology and processes is crucial in maintaining both security and regulatory compliance. By leveraging advanced technology solutions such as AI and ML, entities can significantly enhance threat detection, thereby curtailing potential breaches before they escalate.
The emphasis on automation cannot be overstated; it serves as a powerful ally in policy enforcement, reducing human error while streamlining compliance tasks. Moreover, the establishment of robust incident response plans is vital for addressing data breaches efficiently, a lesson that past incidents clearly illustrate. Regular collaboration with regulatory bodies not only keeps organizations informed about compliance trends but also positions them as informed leaders in a competitive marketplace.
As regulations evolve, a commitment to the continuous review and adaptation of device management policies will enable organizations to remain agile, prepared to tackle emerging threats head-on. This iterative approach ensures that compliance is not just maintained but fortified, allowing organizations to thrive in a digital world fraught with challenges. By investing in these strategies, organizations can protect their assets and reputation while fostering a culture of security and compliance. The path toward effective device management is an ongoing journey, one that promises resilience and security in an increasingly regulated environment.
Related posts:
Automation in Device Management: Effective Tools and Strategies
The Future of Device Management: Trends and Innovations
How to Set Up and Maintain Security on Mobile Devices
Best Practices for Device Management in Corporate Environments
Device Management: How Artificial Intelligence Is Transforming Equipment Administration
How to Efficiently Configure and Monitor IoT Devices
Beatriz Johnson is a seasoned tech writer and digital tools expert with a passion for simplifying the complexities of technology and mobile applications. With over a decade of experience in the tech industry, she specializes in topics like productivity apps, software reviews, and emerging digital trends. Through her work, Beatriz empowers readers to make informed technology choices and stay ahead in the ever-changing world of apps and innovation.